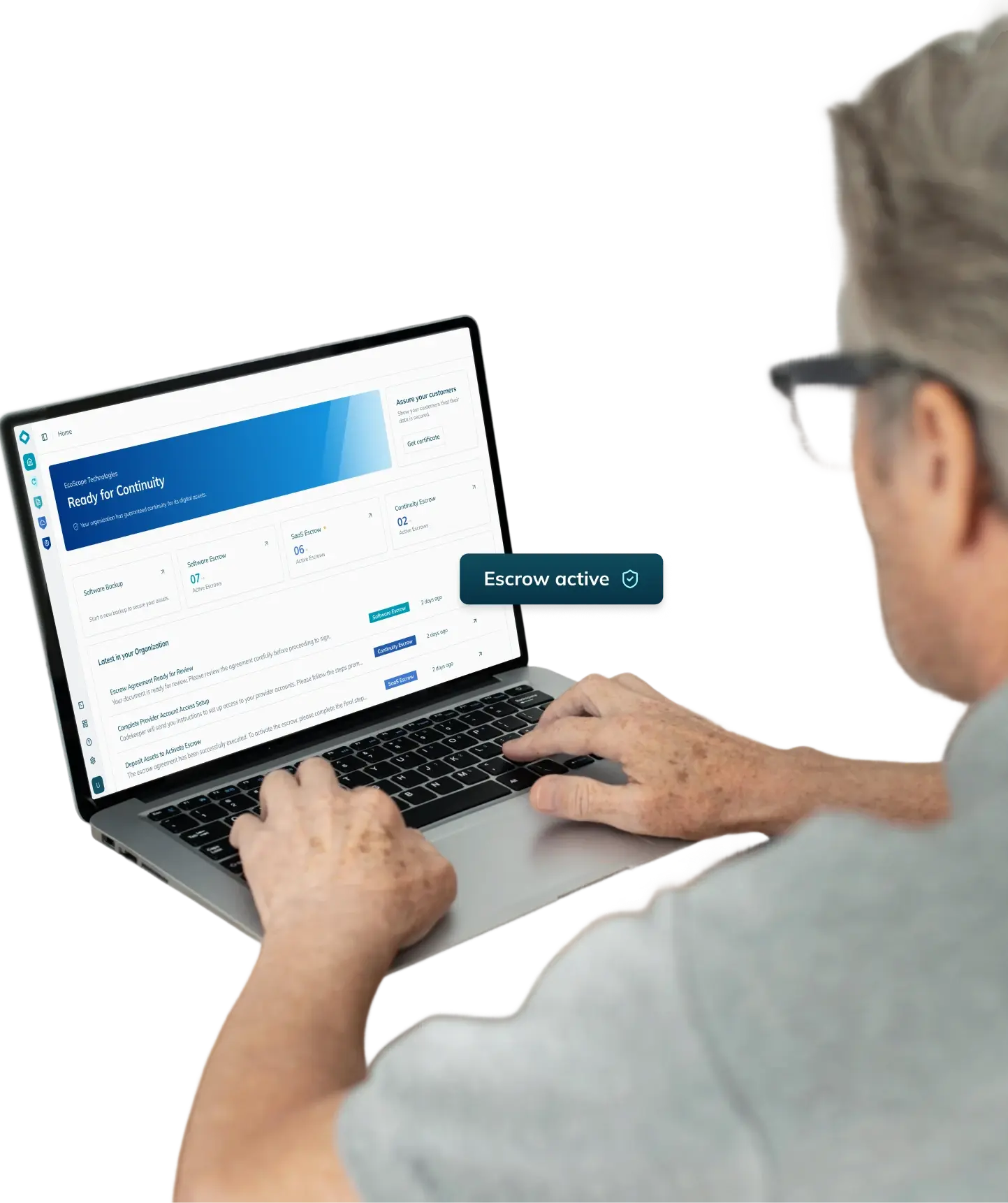
Continuity Escrow
Maintain 100% uninterrupted software access
Do not let hosting or support failures affect your clients. Continuity Escrow keeps you operational, in your market, on your terms.
From
$379
/mo

What happens when the service providers you depend on fail, go bankrupt, or disappear?

What is continuity escrow?
Continuity escrow is a service that keeps your infrastructure operational when payment disruptions occur. When you report a missed vendor payment, Codekeeper maintains the critical service payments on their behalf. This gives you time to transition to new providers or resolve the underlying issue.
Your infrastructure depends on service providers. When they fail, your services go offline. When your services go offline, you cannot serve your clients. When you cannot serve your clients, your business stops.
That’s why continuity escrow protects against:
Hosting suspensions that result from missed payments
System access revoked because accounts expire
Service failures that affect multiple connected dependencies
Lost revenue from being offline during financial transitions
Client abandonment after repeated outages
We keep your systems active during service failures
Every platform your software depends on requires ongoing payments to stay active. This can include APIs, global hosting platforms, or even regional data centers in Asia. If payments on a dependency are missed, we maintain them before your systems go offline. More than 3 500 companies in all major markets around the world rely on Codekeeper’s continuity services. You can too.

How Continuity Escrow works
1. Book a free consultation
Talk with our specialists about your local and global infrastructure dependencies. We will identify which services expose you to risk and explain how they make you vulnerable.
2. Choose a protection level and create your account
Select your plan based on your coverage needs. Then, invite stakeholders to your dashboard. Our in-house legal team will draft your legal framework.
3. Upload your vendors
Link your infrastructure platforms once to activate daily automated synchronization. You can also upload hosting credentials and payment details manually through our secure portal.
4. Verify your software resilience
Order our verification service to test your credentials. We will confirm login access and continuity capability. You will receive a Software Resilience Certificate as compliance proof.
Book a consultation
"Codekeeper is extremely easy to use. In the past, I have struggled with app integrations in Salesforce, but this was easy and really well done. The support is top-notch. The price is reasonable, and the value is high."
Nikki P.
Marketing Manager
What goes into your Continuity Escrow uploads
We protect two asset categories that keep your software operational:

Hosting environments
We store logins for your cloud platforms, dedicated servers, containers, and deployment pipelines. This allows us to access your hosting environments when we need to take over a payment.

Service credentials
We maintain administrative access with credentials, authentication tokens, admin permissions, and API keys. We use this to keep your essential third-party services active when you report a disruption.
Unlimited hosting providers
Unlimited third-party services
Dual-dashboard visibility
Sync any of your infrastructure platforms
Codekeeper supports more than 50 platform integrations from all regions of the world to keep your stored credentials current. Connect your platforms once. Codekeeper will then update your hosting environments, third-party service credentials, and critical infrastructure details every day.




View all integrations
Full-service legal and technical support
Continuity protection requires precisely configured technical systems and accurate legal agreements that account for intricate regulatory regions, like China or South Korea. We manage both so that the implementation is conducted correctly from the start.

Legal framework included
We draft continuity agreements for your specific business needs. You can choose between agreement templates or completely custom contracts for unique infrastructure arrangements that accommodate global partners.

Multi-party arrangements
Your agreement can involve two parties, three parties, or multiple vendors. We define payment triggers, service responsibilities, and activation protocols for everyone involved.

Jurisdiction selection
Choose the legal jurisdiction that makes sense for you. Whether you operate regionally in Asia or across borders, we can tailor your agreement to your existing contracts and specific regulatory requirements.

Service continuity coverage
If vendor payments stop, your essential services keep operating for up to 12 months. This gives you enough time to implement long-term solutions.

24/7/365 event processing
Service disruptions can happen at any time. You can contact us 24/7 over phone, chat, or email. We process immediate activation requests at per hour.
Unique in-app agreement management
24/7 technical and legal support
Guided implementation
Continuity services built on invulnerable security and verified for trust
Storing hosting credentials and administrative access demands serious security. We provide the protection auditors and stakeholders from all international markets expect, with the documentation they require.

AES-256/512 encryption
Military-grade encryption protects your credentials and access tokens during the upload process, storage, and activation.

Access logs
A permanent record captures what was uploaded, any changes made, and who authorized modifications. This log gives compliance teams a complete and unalterable history of all credential activity.

Multi-factor authentication access control
You can control exactly who can access your credentials by adding two-factor authentication for sensitive roles. Detailed logs record every access attempt so your team can review activity at any time.
Global secure vault network
Immutable storage
Software Resilience Certificates included
Guarantee your continuity capability with technical testing
Continuity Escrow keeps your services operating when payments fail. But regulators and auditors still want to see documented proof that your systems will remain resilient.

Validated
FREE
Our automated systems confirm that all required credentials exist in your uploads.
Includes: Basic Software Resilience Certificate

Verified
We activate continuous checks that confirm your escrowed credentials remain current. We provide monthly credential reports.
Includes: Enhanced Software Resilience Certificate

Certified
Technical staff use your escrowed credentials to conduct service restoration simulations. This confirms system access and activation readiness.
Includes: Premium Software Resilience Certificate
Compare all verification levels
If providers support your infrastructure, activating Continuity Escrow is the right decision.
Dependencies create operational risk. Talk with our continuity specialists about eliminating these vulnerabilities so that your services are always online. Your consultation will cover:
Infrastructure vulnerability assessment
A guided continuity implementation plan
Answers to your technical and legal questions
Need protection for other software types?
Explore our complete software resilience platform.

Software Backup
Automated daily backups of your internal applications with unlimited storage capacity.
Learn more

Software Escrow
Secured source code and documentation to protect your on-premises applications.
Learn more

SaaS Escrow
Cloud application protection that includes your code, data, and deployment configurations.
Learn more

AI Escrow
AI stack protection that secures your training assets, prompts, and inference infrastructure.
Learn more
Frequently asked questions
How does Continuity Escrow help you build digital resilience?
How does Continuity Escrow help you build digital resilience?
Continuity Escrow prevents operational downtime caused by missed payments. When a critical infrastructure bill goes unpaid, you report the problem, and we immediately take over the payment. Your hosting stays active, your services remain funded, and your applications stay operational. This gives you time to find a long-term solution.
What proof of protection does a Continuity Escrow provide?
Every Continuity Escrow account includes a basic Software Resilience Certificate at the Validated level. This certificate proves your protection is active. If you need stronger verification, you can upgrade to an Enhanced certificate at the Verified level or a Premium certificate at the Certified level. These higher tiers include testing to confirm your credentials work and that we can activate your services when needed. All three certificates give your auditors, clients, and stakeholders documented proof of your operational resilience.
How quickly can Continuity Escrow activate if a payment issue occurs during Asian business hours?
Continuity Escrow is designed for 24/7 use across all time zones, including Asia‑Pacific working hours. When you report a payment issue, our team processes activation requests immediately through our emergency channel — no matter where you are or what time it is.
What makes Continuity Escrow different from traditional software escrow?
Traditional software escrow stores source code so you can recover after a disruption occurs. Continuity Escrow stores service credentials and supporting information so we can intervene before a disruption can affect your operations. When you report a missed payment, we maintain it immediately. Your services stay active, and your operations continue without interruption.
Is Continuity Escrow the same as cyber insurance?
No. Cyber insurance compensates you financially after an operational failure causes losses. Continuity Escrow prevents those failures from occurring. We maintain your services during payment disruptions so you do not experience the downtime that would trigger an insurance claim. Many businesses use both. Insurance covers financial impact, while Continuity Escrow gives you time to find a long-term solution.