Software Escrow
Secure your access to on-site software
Verified software escrow vaults protect your source code, data, and documentation — with certified recovery trusted by organizations across Asia, Europe, and the Americas.
From
$129
/mo

What happens when the software you depend on fails, breaks, or is attacked?

What is software escrow?
Software escrow is a three-party agreement between vendors, users, and Codekeeper. Vendors deposit source code, data, and documentation. We secure these materials. When specified failure conditions occur, we release the materials so users can maintain the software independently.
Your software depends on vendors. When they fail, your software breaks. When your software breaks, you cannot serve your clients. When you cannot serve your clients, your business stops.
That’s why software escrow guards against:
Vendor bankruptcy that removes support without warning
Product discontinuation that forces costly migrations
Security vulnerabilities you cannot fix with your own resources
Contract disputes that stop your operations
Lost enterprise deals due to missing continuity guarantees
We make sure your software never stops working
Your on-premises software supports every business process for every client each day. That is why we protect source code for the software that supports your business. Codekeeper is trusted by 3 500+ businesses across various global markets. You can rely on us too.

How Software Escrow works
1. Book a free consultation
Talk with our escrow specialists about your software dependencies. We can identify which of your assets to secure. We will also explain exactly how escrow protects your interests.
2. Choose a protection level and create your account
Select a plan and verification tier. Then add your team members. We configure your vault and customize your agreement framework to your requirements.
3. Deposit your software materials
You can connect your repositories for automatic daily synchronization. Or you can upload your materials manually. We support both.
4. Certify your software resilience
We examine your deposits to confirm their completeness and test your recovery readiness. We then issue a Software Resilience Certificate for compliance proof.
Book a consultation
"Codekeeper lifted us at every turn, from setting up the escrow agreement, handshaking the agreement with all parties, and using the tool to get the repositories in sync. I would spotlight the portal that walks you through each step — it builds trust for us and our clients alike — plus the technical setup that enables our teams to share code effortlessly. That combination simplifies everything and saves us real effort."
Paul T. *
Senior Managing Director
* Pseudonym used to maintain customer confidentiality.
What goes into your Software Escrow deposits
On-premises software escrow protection requires three essential asset types:

Source code
The whole codebase required to build and deploy your application.

Data
The databases, records, and information assets your software needs to operate.

Documentation
Technical knowledge used to transform source code into operational software.
Automated daily syncs
Unlimited deposits included
Dual-dashboard visibility
We sync with your systems
Codekeeper supports 50+ integrations to make it easy for you to add and manage your repositories. You only need to connect your platforms once. We sync your source code, data, and documents daily. You will not need to manage releases and versions manually or decide which repository belongs where.
View all integrations



Complete legal and technical support
Getting escrow protection right requires legal expertise of all jurisdictions involved and technical know-how. We provide both to make implementation straightforward.

Legal framework included
Our legal team drafts escrow agreements according to your specific needs. We offer standard templates and fully custom arrangements.

Multi-party arrangements
We structure bi-party, tri-party, and multi-party agreements with clearly defined release conditions, verification requirements, and legal obligations.

Jurisdiction selection
Your escrow agreement operates under the jurisdiction that aligns with your business requirements, contracts, and regulatory obligations.

24/7/365 event processing
Contact us anytime by phone, chat, or email for urgent releases. Our release processing service is available 24 hours a day, 7 days a week, and costs per hour.
Unique in-app agreement management
24/7 technical and legal support
Guided implementation
Premium security and compliance standards
Securing sensitive source code requires the highest-tier security infrastructure and documentation that can comply with global regulatory audits. We built our vaults for both.

AES-256/512 encryption
All deposits are encrypted during transfers and storage using military-grade encryption standards.

Version history
Every deposit is logged, and all changes are recorded. You can also preserve every version of your deposits with full audit trails.

Multi-factor authentication access control
You gain complete permission control over who can see what. Make use of role-based access and detailed audit logs to record every action made in your repository.
Global secure vault network
Immutable storage
Software Resilience Certificates included
Prove your deposits are ready for recovery
Software escrow deposits need verification. Without it, you cannot confirm that your deposited materials are complete and usable.

Validated
FREE
We conduct automated checks to ensure all your essential materials are present in the deposit.
Includes: Basic Software Resilience Certificate

Verified
We set up automated monitoring to validate the file integrity and content structure of your escrowed materials. You receive monthly activity reports.
Includes: Enhanced Software Resilience Certificate

Certified
Full technical build tests and expert reviews are conducted to ensure the deposits can be used for a recovery.
Includes: Premium Software Resilience Certificate
Compare all verification levels
If software supports your business, activating Software Escrow is the right decision.
Do not risk a software shutdown. Talk with our escrow specialists about securing your on-premises systems and how we will accommodate your regional legal requirements. Your consultation includes:
Risk assessment from escrow experts
Implementation roadmap
Answers to your legal and technical questions
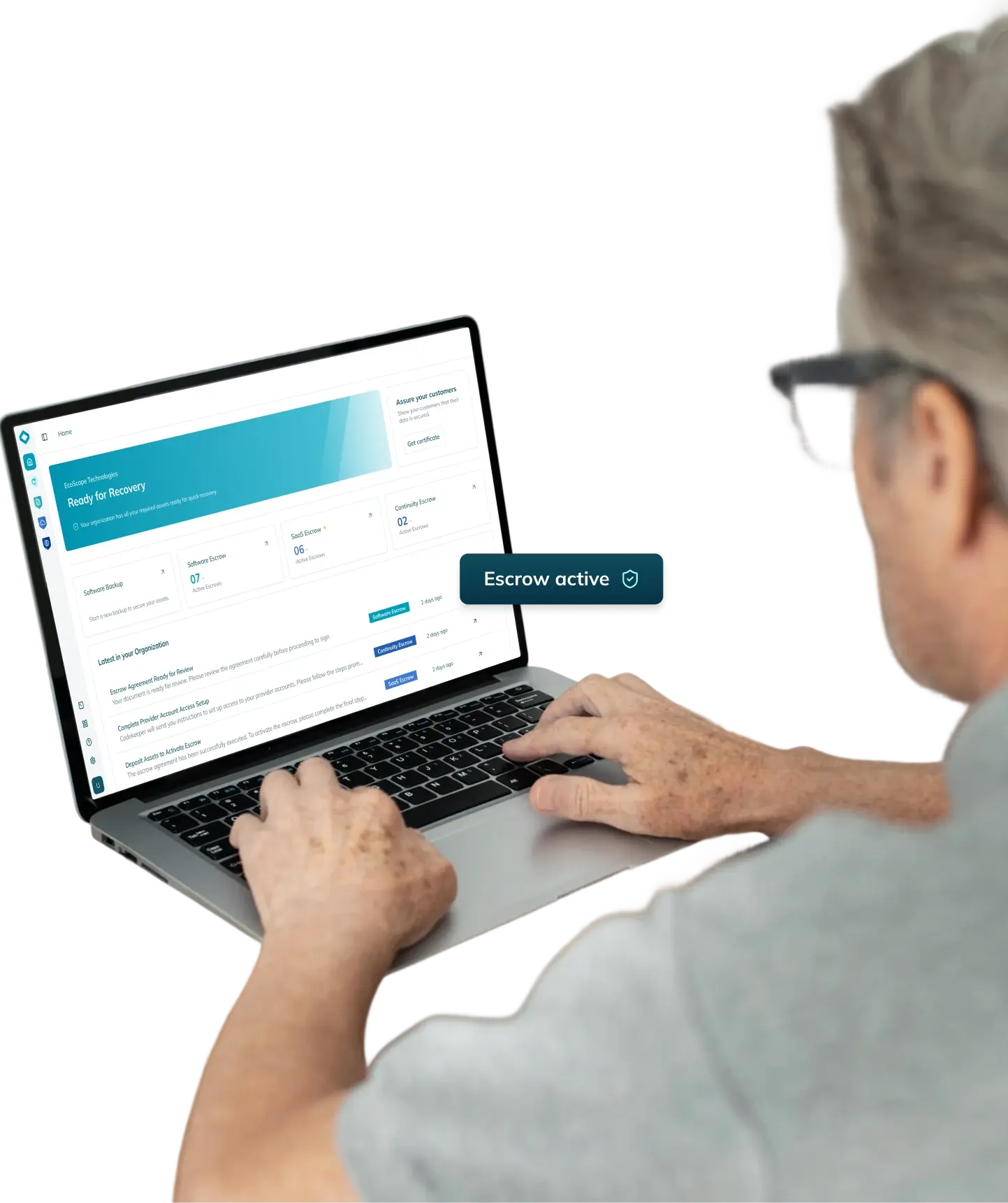
Need protection for other software types?
Explore our complete software resilience platform.

Software Backup
Automatic daily backups of your internal systems with unlimited storage.
Learn more

SaaS Escrow
Maintained access to cloud application components and deployment assets for recovery.
Learn more

AI Escrow
Complete protection for your AI stack, including models and training assets.
Learn more

Continuity Escrow
Access protection for supporting and hosting services to keep critical applications online 24/7.
Learn more
Frequently asked questions
What is software escrow?
Software escrow is a legal arrangement that protects licensed software users by ensuring continuous access to the software's source code and other critical materials. In a software escrow agreement, the software developer or vendor deposits a copy of the source code, documentation, and other essential components with a trusted third-party escrow agent, such as Codekeeper. This agent securely stores and manages these materials on behalf of the software provider and the beneficiary.
How does Software Escrow help you build digital resilience?
Software Escrow strengthens digital resilience by storing your on-premises software assets in a secure vault. If your live systems fail, you can restore operations quickly and maintain compliance without disruption.
For what purpose is Software Escrow most commonly used?
Businesses use Software Escrow to protect on-premises applications. Escrow guarantees access to source code and critical assets. So vendors can prove reliability to their clients. And clients can maintain operations even if an unexpected problem occurs with their vendor.
What is a software escrow agent?
A software escrow agent is a neutral third party, like Codekeeper, who securely stores your software materials. We manage deposits, verify usability, and release assets when agreed conditions are met. This protects your ability to recover and continue operations.
What is protected by a software escrow agreement?
A software escrow agreement protects source code, application data, technical documentation, and your intellectual property.
Can Software Escrow reflect different legal systems and contract laws?
Yes. Software escrow agreements can be written to reflect the law and contract practices of the jurisdiction you choose. This matters when your software relationship crosses borders, for example, if your company is based in China and you want to secure continued access to software from a vendor in the United States. Release conditions, notice periods, and permitted uses of released materials can all be adjusted so they fit the legal expectations on each side while still giving you a clear path to continue using the software when something goes wrong.
What are the release conditions for a software escrow agreement?
Release conditions refer to specific events that trigger the legal clauses for the release of deposited materials. This can be events like vendor bankruptcy, discontinued support, or contract breaches. When a release condition occurs and is confirmed, we provide immediate access to the deposited materials.
What proof of protection does Software Escrow provide?
You get a free basic Software Resilience Certificate with your Software Escrow plan. This documentation proves to clients, auditors, and regulators that your materials are secure and validated.
What are the benefits of Software Escrow?
Software Escrow protects your organization in three ways. First, it reduces legal costs. Our in-house legal team drafts your escrow agreement at no extra cost. This saves your organization up to $5,000 in external legal fees. Second, it reduces technical work. Daily automated syncs remove the need for manual deposits. This saves your development team 40+ hours of DevOps work. Third, it guards your software assets. All deposits are protected with AES256/512 encryption. So your source code, data, and documentation are secure at all times.
Do we need Software Escrow if we have a disaster recovery plan in place?
Yes, because disaster recovery plans often lack source code access. Software Escrow solves that issue by securing code and data for on-premises apps. This cannot be done with normal backups.