Multi-layered software protection for your system risks


You protect your data. You protect your customers. Who is protecting your software?
Codekeeper guards your software against all risks
Software failure
Cyber attacks
Non-compliance
Broken software
Work with us to eliminate your software risk


Software resilience solutions for every department

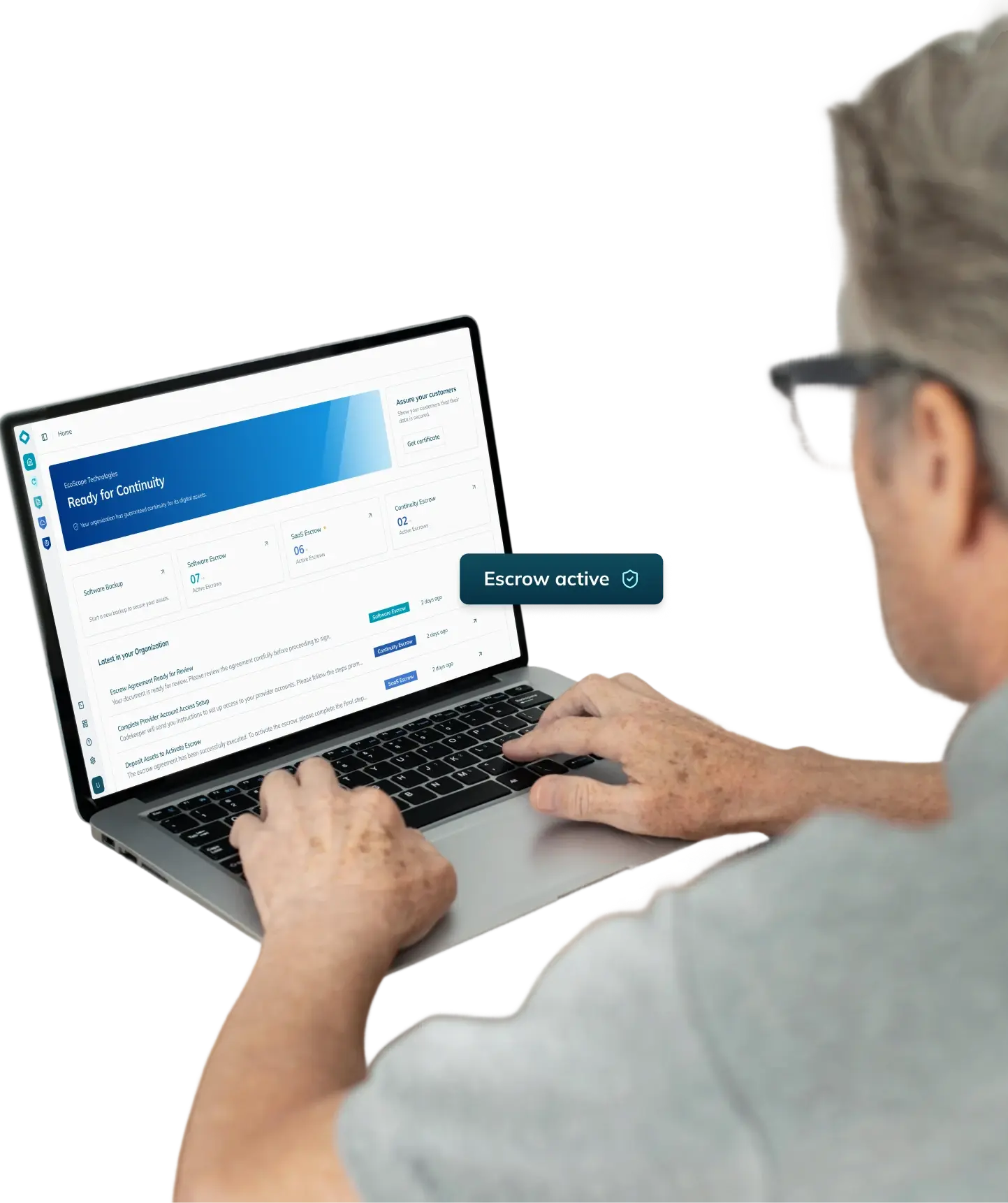
Management teams get full visibility and control
Compliance members get documented proof

Legal departments get flexible agreements

DevOps divisions get full automation

Security branches get military-grade encryption and tamper-proof storage

Finance and procurement teams get transparent pricing
Find the right protection solution for your software
Access what you need when failures happen
Software Backup
Software Escrow
SaaS Escrow
AI Escrow
Keep systems online during disruptions
Continuity Escrow
Custom Escrow
Prove your protection works
Validated
Verified
Certified
3 500+ companies already protect their software with Codekeeper. You can too.
I'd highly recommend Codekeeper. They clearly understand the realities of working with growing tech businesses and enterprise customers alike.”
If your software is not protected, activating software resilience is the right decision.
Frequently asked questions
How does software escrow work?
Software escrow works through a legal agreement between three parties. These parties include the software vendor, the software buyer (called the beneficiary), and an escrow agent (a neutral third party, such as Codekeeper).
Here is how the process works:
- The software vendor deposits materials with the escrow agent. These materials include source code, documentation, and build instructions.
- All three parties sign an escrow agreement. This agreement defines the conditions under which the materials will be released.
- The escrow agent stores the materials securely. Deposits are updated on a regular schedule.
- If a release condition occurs (for example, vendor insolvency or discontinued support), the beneficiary requests a release. The escrow agent reviews the request. If the condition is confirmed, the agent releases the materials to the beneficiary.
How does software escrow reduce business risk?
Software escrow reduces risk for both software buyers and software vendors.
For buyers, escrow guarantees access to the source code your organization depends on. If your vendor can no longer support you, you can continue operations independently or through another provider.
For vendors, escrow proves you are a safe and reliable choice. Buyers are more likely to sign contracts with vendors who can demonstrate continuity guarantees.
For both parties, escrow also reduces compliance risk. Regulators require documented proof that critical systems can recover from failure. Codekeeper provides that proof through Software Resilience Certificates and audit logs.
Under local copyright law, how far can we use source code released through escrow?
The permitted use of released source code depends on the jurisdiction your agreement covers and the terms written into it. In most cases, release grants the right to continue operating the software for business continuity. The specific scope varies by region.
Codekeeper's legal team drafts all escrow agreements with jurisdiction-specific terms included. If your business operates across multiple regions, we structure your agreement to meet the legal requirements of each market. So when a release occurs, you can act on it immediately.
What is an application in the context of SaaS Escrow?
In SaaS Escrow, an application refers to the complete environment that delivers your cloud-based service. It includes source code databases, access credentials, third-party integrations, and deployment configurations and scripts.
How does escrow help vendors win enterprise deals?
Enterprise clients often require proof that their software investments are protected before they sign a contract. Software escrow provides that proof. When a vendor offers escrow protection, enterprise clients see this as evidence of professional risk management. It shows that the vendor is committed to long-term service continuity.
For smaller vendors, escrow removes one of the biggest obstacles in enterprise sales. It addresses the client's concern about what happens if the vendor faces difficulties. And it helps close deals faster because procurement teams have the documentation they need.
How quickly can source code protection be set up?
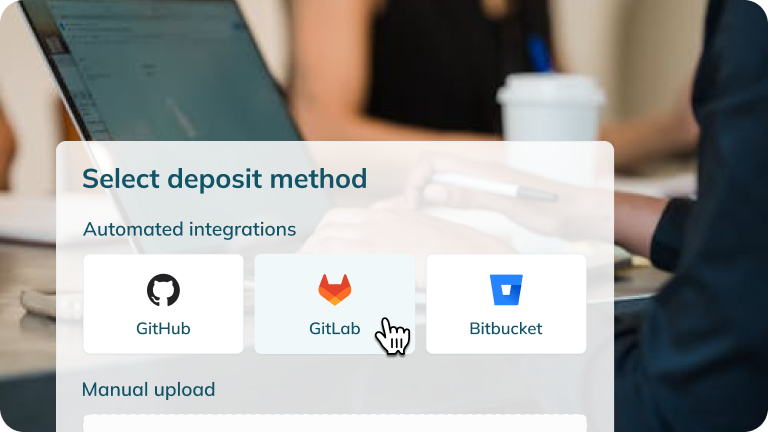
Codekeeper can set up source code protection within 24 hours. Our platform connects directly to your repositories through secure integrations. We support GitHub, Bitbucket, AWS, and other major platforms. The connection is set up once. After that, your deposits update automatically.
For the legal framework, our in-house legal team will draft your escrow agreement between one and three days.